How being hacked impacted our startup’s key metrics
CEO and co-founder @ Buffer
Buffer was hacked on October 26th, resulting in several thousand spam posts appearing on Twitter and Facebook. Here is the impact on our numbers.
Last Saturday I was sitting in my favorite coffee shop doing a few support tickets and writing a blog post when I opened Facebook and saw that the whole of my timeline was full of spam. The next thing I noticed was that all of the spam was “via Buffer”. I scrolled and scrolled and it was endless.
We’ve written a lot about what actually happened and how to get your account running smoothly again. You probably saw news of the security breach if you read any of the tech and startup news sites.
It took a whole week, but it seems we have managed to weather the storm. We’re continuing to ramp up security in all areas of the product and company. When I had a moment to breathe I was keen to assess the impact so I started running some queries. Here is what I found:
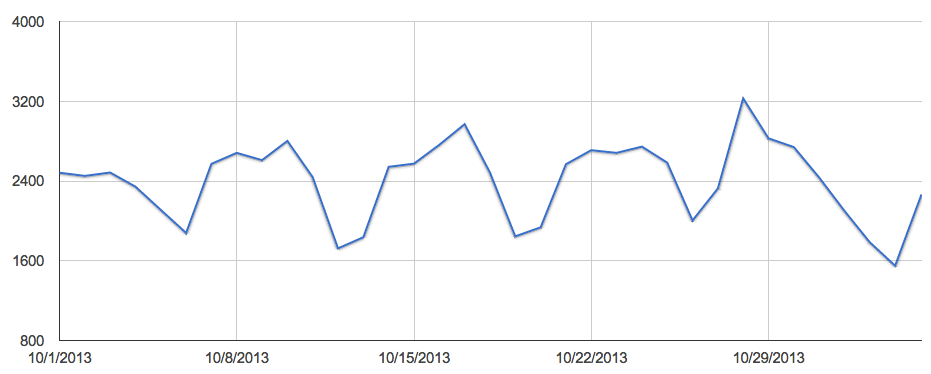
Posts sent per hour by Buffer users
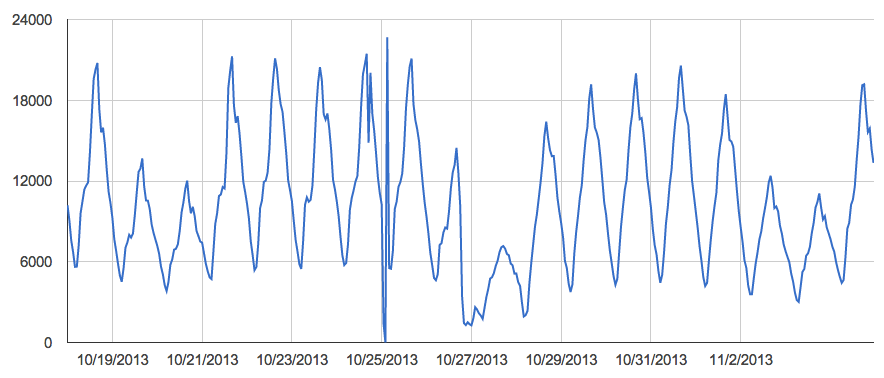
Note: The dip around the 25th was a separate issue (a bug we accidentally introduced) that resulted in delayed posts.
As you can see, normal posting volume dropped significantly in early hours of the 27th, right around the time of the spam attack.
Posts sent per day by Buffer users
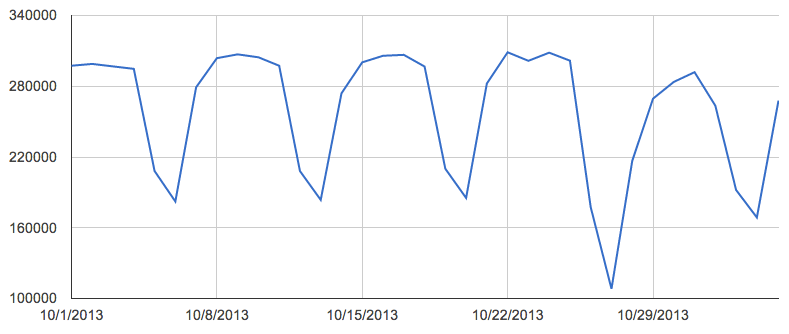
This chart shows the real impact more clearly. We saw a big decrease in posts sent with Buffer around the hacking incident.
Interestingly, posting volume has returned almost to normal levels after just a few days.
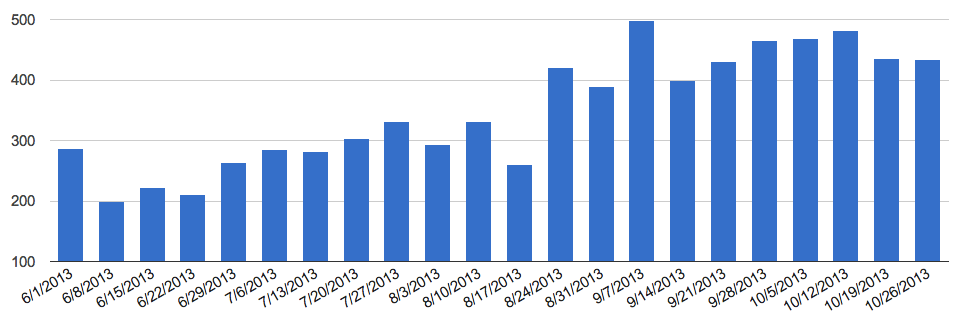
Weekly downgrades from the paid plan since June
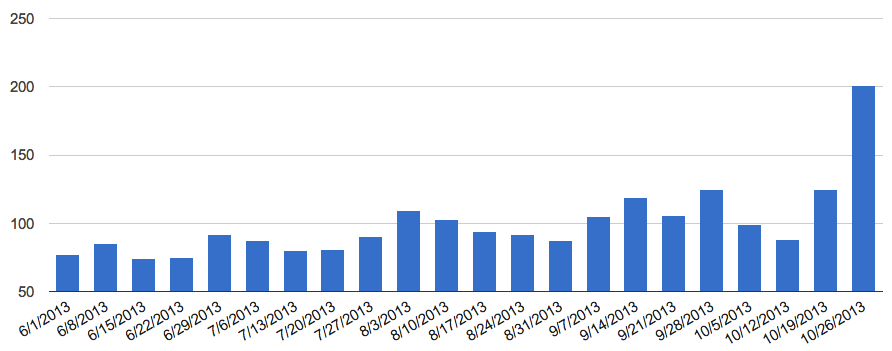
The number of downgrades from the $10/mo paid Buffer plan spiked in the week of the hacking incident.
The increase that week is 1.6x the normal number of downgrades we see.
Daily downgrades from the paid plan since October 1st
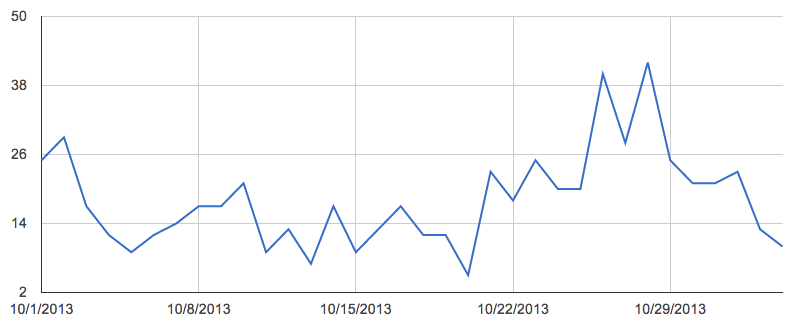
This shows useful additional information from the weekly chart above.
Most notably, while there was a real spike in the few days of the spam attack, daily downgrades dropped sharply back to normal levels.
Daily signups since October 1st
This signups chart is one of the most interesting. The fascinating thing is that during the few days of our breach, we had almost record numbers of signups. This is perhaps due to our fortunate scenario of receiving positive press around how we handled the breach.
In the week that follows, our signups have dipped quite a lot. My hypothesis for this is that we halted our regular content marketing efforts on the main Buffer blog in order to focus on the investigation of the hacking incident.
Weekly upgrades to the paid plan since June
This chart shows that upgrades to our paid plan are almost completely unaffected by the hacking incident. It seems like the breach didn’t cause people to not upgrade to the Awesome Plan. You can see in the chart that we received almost exactly the same number of upgrades in the week of the hacking compared to the week before.
I hope these insights might be interesting. Let me know if there’s anything else you’re curious about and I’ll see if I can dig up the stats!
Try Buffer for free
140,000+ small businesses like yours use Buffer to build their brand on social media every month
Get started nowRelated Articles

TikTok's parent company must divest the app or face a ban in the U.S. Here's everything we know, plus how to plan ahead.

How the Buffer Customer Advocacy Team set up their book club, plus their key takeaways from their first read: Unreasonable Hospitality by Will Guidara.
In this article, the Buffer Content team shares exactly how and where we use AI in our work.